1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
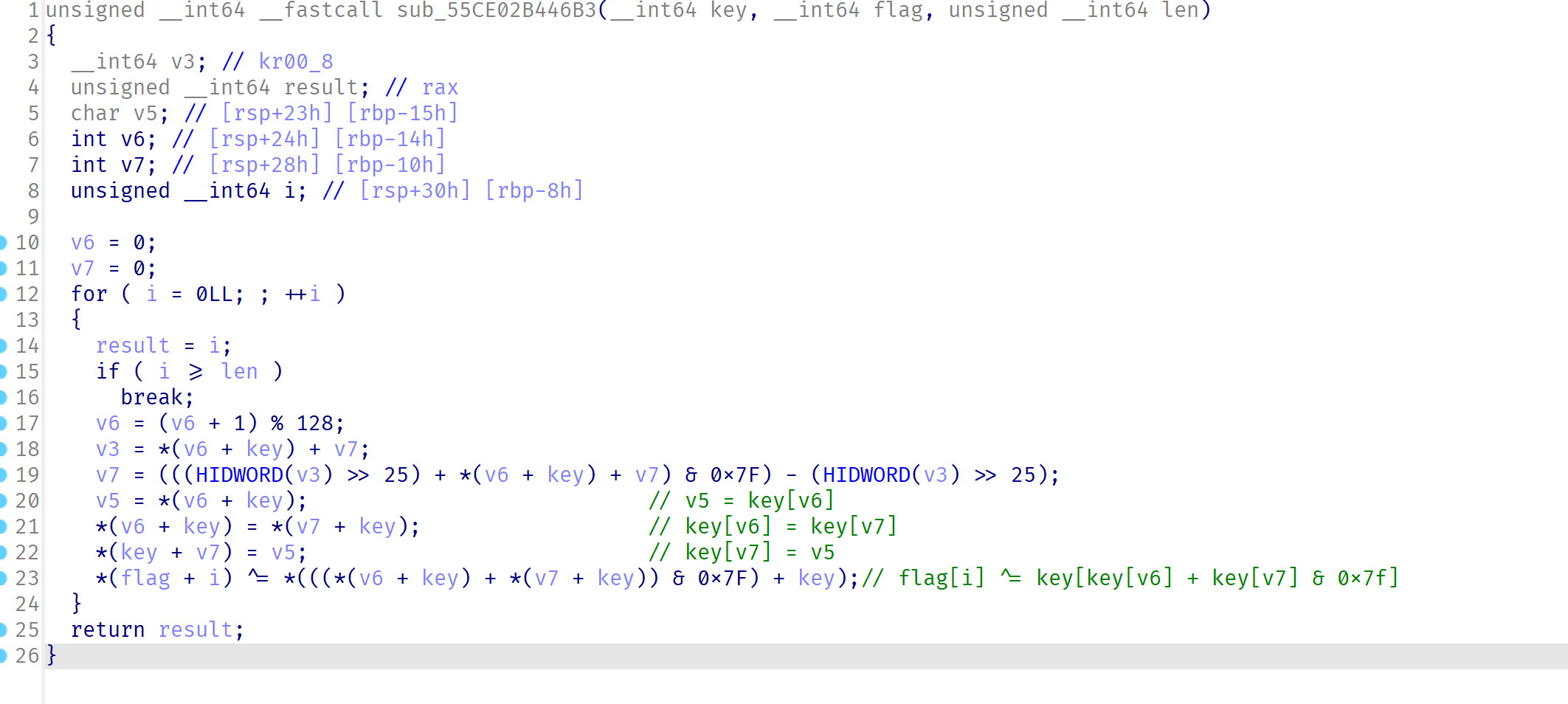
| #include <iostream>
#include <stdint.h>
#define HIDWORD(x) ((uint32_t)(((uint64_t)(x) >> 32) & 0xFFFFFFFF))
int main() {
int v6; // [rsp+24h] [rbp-14h]
int v7; // [rsp+28h] [rbp-10h]
unsigned __int64 i; // [rsp+30h] [rbp-8h]
int v3;
int v5;
int len = 21;
v6 = 0;
v7 = 0;
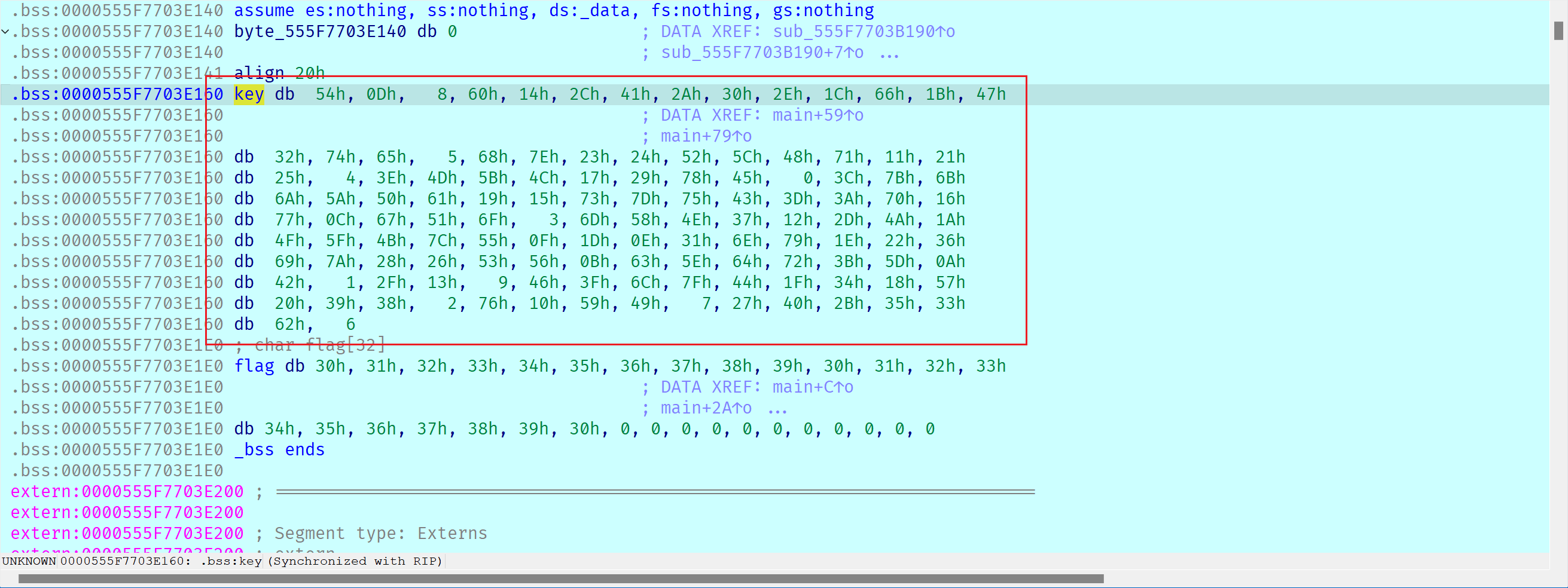
unsigned char key[128] = {
0x54, 0x0D, 0x08, 0x60, 0x14, 0x2C, 0x41, 0x2A, 0x30, 0x2E, 0x1C, 0x66, 0x1B, 0x47, 0x32, 0x74,
0x65, 0x05, 0x68, 0x7E, 0x23, 0x24, 0x52, 0x5C, 0x48, 0x71, 0x11, 0x21, 0x25, 0x04, 0x3E, 0x4D,
0x5B, 0x4C, 0x17, 0x29, 0x78, 0x45, 0x00, 0x3C, 0x7B, 0x6B, 0x6A, 0x5A, 0x50, 0x61, 0x19, 0x15,
0x73, 0x7D, 0x75, 0x43, 0x3D, 0x3A, 0x70, 0x16, 0x77, 0x0C, 0x67, 0x51, 0x6F, 0x03, 0x6D, 0x58,
0x4E, 0x37, 0x12, 0x2D, 0x4A, 0x1A, 0x4F, 0x5F, 0x4B, 0x7C, 0x55, 0x0F, 0x1D, 0x0E, 0x31, 0x6E,
0x79, 0x1E, 0x22, 0x36, 0x69, 0x7A, 0x28, 0x26, 0x53, 0x56, 0x0B, 0x63, 0x5E, 0x64, 0x72, 0x3B,
0x5D, 0x0A, 0x42, 0x01, 0x2F, 0x13, 0x09, 0x46, 0x3F, 0x6C, 0x7F, 0x44, 0x1F, 0x34, 0x18, 0x57,
0x20, 0x39, 0x38, 0x02, 0x76, 0x10, 0x59, 0x49, 0x07, 0x27, 0x40, 0x2B, 0x35, 0x33, 0x62,0x06
};
for ( i = 0LL; ; ++i )
{
if ( i >= len )
break;
v6 = (v6 + 1) % 128;
v3 = *(v6 + key) + v7; // v3 = key[v6] + v7
v7 = (((HIDWORD(v3) >> 25) + *(v6 + key) + v7) & 0x7F) - (HIDWORD(v3) >> 25);
v5 = *(v6 + key); // v5 = key[v6]
*(v6 + key) = *(v7 + key); // key[v6] = key[v7]
*(key + v7) = v5; // key[v7] = v5
printf("%d,",*(((*(v6 + key) + *(v7 + key)) & 0x7F) + key));// flag[i] ^= key[(key[v6] + key[v7]) & 0x7f]
} // key[v7] = v5
}
//105,80,32,18,9,17,58,107,45,32,87,66,88,25,63,99,80,56,12,95,94,
|